Multi-Factor Authentication
Weak and compromised passwords are invovled in most cybercrime cases. Improve your security by leveraging Teamstack'sTM Multi-Factor Authentication.
Build Your TeamIt's free. No credit card required.
Multiple Factor Types
Apply different authentication factors ranging across different security levels across your whole organization to protect against unauthorized access while providing flexibility for users.
- WebAuthn (FIDO2)
- TOTP (Google Authenticator)
- SMS Code
- Security Questions
- Recovery Codes
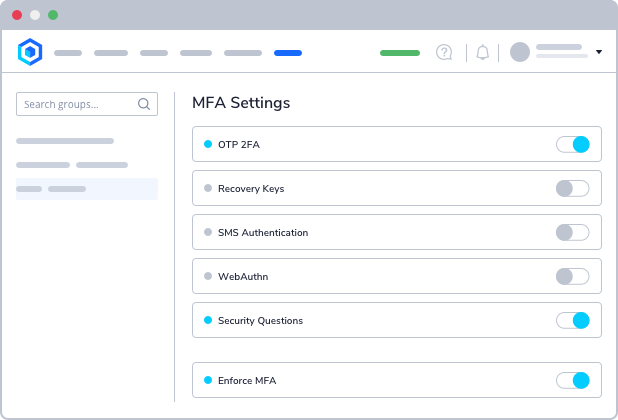
Policy Based MFA Enforcement
Set user or application policies to implement additional authentication factors for sensitive applications or users to restrict access to only those who need it. Specify password requirements for all or specific users.
- Geo-Location
- IP Whitelist
- IP Blacklist
- Biometrics
Prevent Unauthorized Access
Secure your company data from unathorized access and protect yourself from identity attacks by defining failed MFA challenges before users get locked out.
Context Based Denials
Completely restrict access to applications that contain sensitive data based on contextual factors to deny access from high-risk locations or IP addresses.
- Audit Trail
- Incident Reporting